
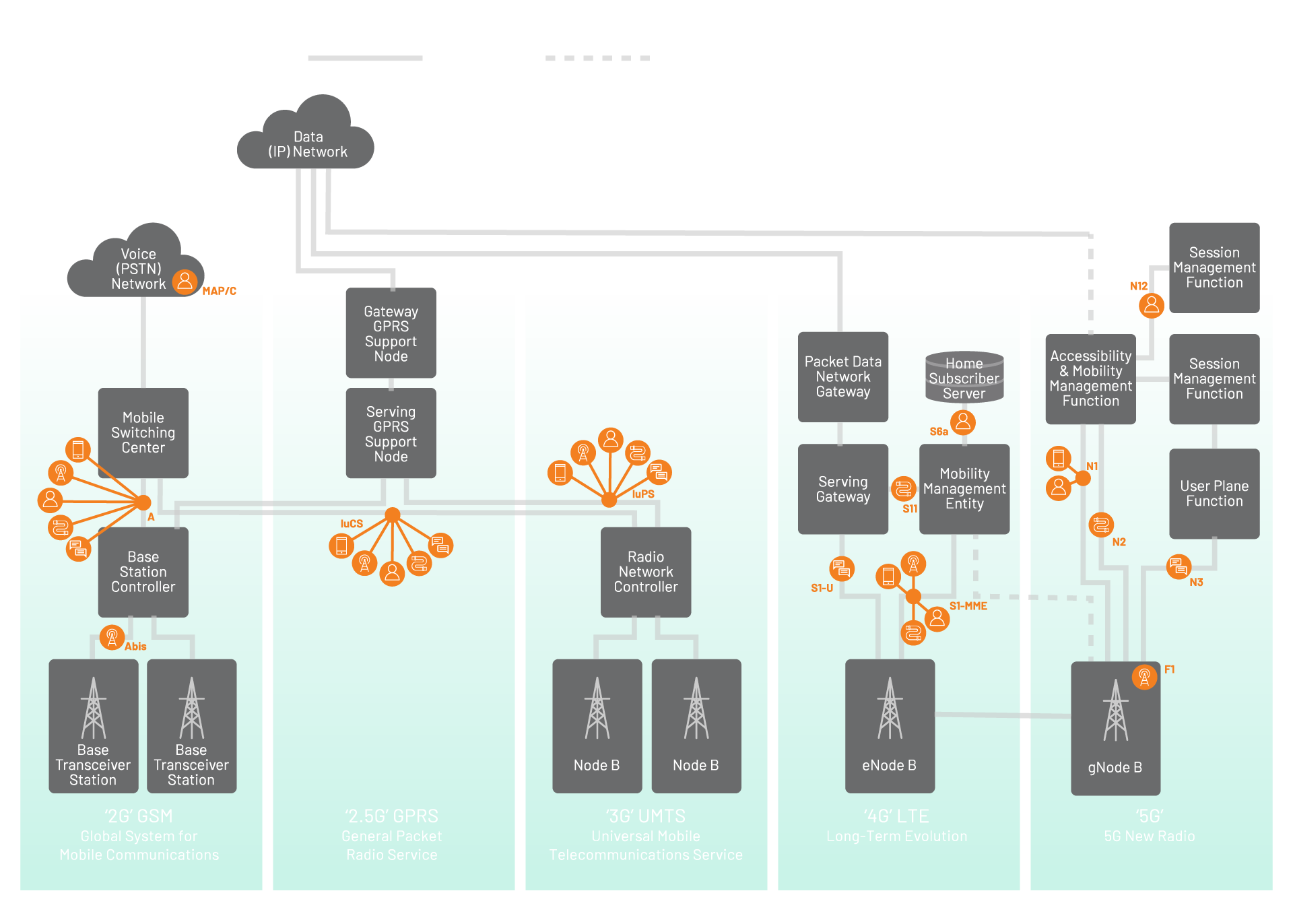
Our mobile communications landscape is becoming increasingly complex. New technologies are being developed to meet consumers’ demands for more services and increased data rates. Meanwhile, critical infrastructure still relies on previous generations of mobile networks for machine-to-machine communications.
Against this backdrop, the need for effective collection for the intelligence community and law enforcement remains paramount. However, this can prove challenging as networks are becoming more multi-faceted, with equipment from different vendors, the advent of virtualization and cloud-based services, and the relentless increase in the speed and volume of transmitted data.
Mobile Collect from Illuminate provides a comprehensive solution for the collection and processing of cellular data across all generations of networks and system manufacturers. Illuminate’s technology supports your compliance with all legal requirements, captures all relevant information, and most importantly, provides the insight that keeps us all safe.

| DEVICE | IMEI/PEI | Identify devices with weak or obsolete encryption |
|---|---|---|
| Radio Capabilities | Identify devices that have been modified | |
| Security Capabilities | Identify unauthorized or untested devices |
| RADIO | Cell Identifier | Indentify movement patterns |
|---|---|---|
| Tracking Area | Identify coverage gaps | |
| Access & Handovers | Identify interference and malicious base stations |
| IDENTITY | IMSI/SUPI | Track user sessions across multiple accesses |
|---|---|---|
| SUCI | Find permanent associated with temporary ID discovered via RF scanning | |
| TMSI/GUTI |
| BEARER | Requested QoS | Compare intended QoS against measured experience |
|---|---|---|
| Slice Identifier | Identify traffic associated with mission critical services | |
| Endpoint Identifiers | Cue active devices in user plane to block malicious traffic |
| Session | Call Parties | Perform traffic analysis to build patterns of life vulnerabilities with outdated certificates ML assisted tracing of encrypted communications |
|---|---|---|
| Call Routing | ||
| Host Identifiers |
+1 (703) 659 9965
198 Van Buren Street, Suite 200
Herndon, Virginia 20170
United States of America
Apex 2, 1st Floor
97 Haymarket Terrace
Edinburgh EH12 5HD
United Kingdom